KEEP YOUR MICROSOFT EXCHANGE SAFE WITH VMHOSTS
A new vulnerability has been discovered in Exchange. It’s only been a few months since the last Vulnerability but again it’s crucial to get your Exchange servers patched ASAP. This latest vulnerability seems to have first been realised by security researcher .
The issue has since been tracked by the ZeroDayInitiative and later Microsoft.
What’s the risk to my business?
It’s currently unclear how much this new vulnerability is being exploited and how many threat actors have working exploits, experience tells us that it will not be a long wait to see exploits in the wild. If you have an exchange server, even if it is hybrid, and it is connected to the internet then there is a chance your environment could be breached. Once inside, threat actors can steal data or destroy data, putting your staff, customers and business at risk!
What is a Zero Day?
“Zero day” is used to describe a recently discovered security vulnerabilities that hackers can use to attack systems. The term “zero day” refers to the fact that the vendor or developer has only just learned of the flaw – which means they have “zero days” to fix it. A zero day attack takes place when hackers exploit the flaw before vendors, Microsoft in this case, have a chance to address it. The result of this is that it becomes much harder to protect against.
How VMhosts can help?
VMhosts can monitor and patch your environment proactively so you don’t have to worry about things like this. We make managed clients secure as a first priority and help keep everyone else secure. Whether you need help securing your environment, backing it up or help with a DR planning, we are here to help.
The technical bit!
Whilst Microsoft have not yet released a patch there are mitigations published which help remove the risk:
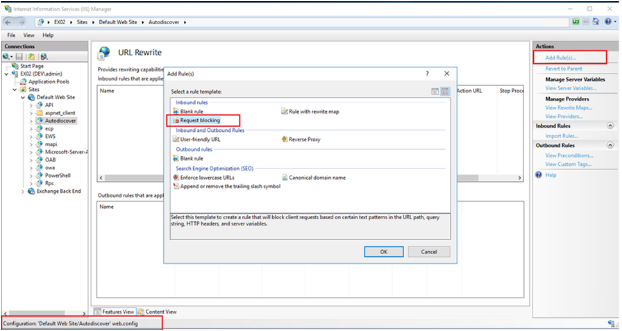
– Have the URL Rewrite module installed in IIS
– In Autodiscover at FrontEnd select tab URL Rewrite, select Request Blocking
– Add string “.*autodiscover\.json.*\@.*
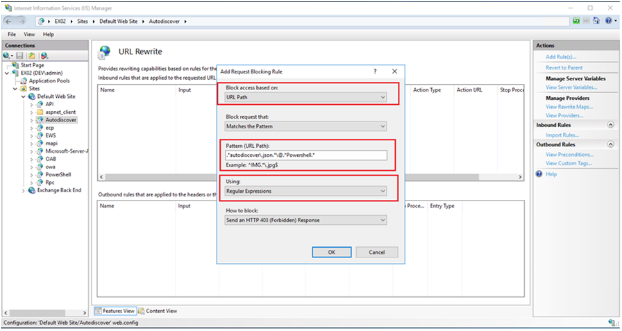
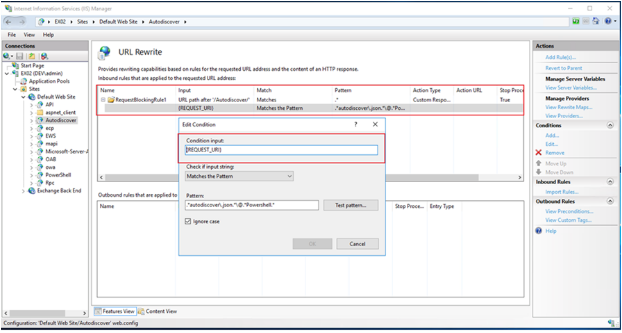
– Condition input: Choose {REQUEST_URI}
If you get stuck at any point why not call our skilled staff for help!
